IPv6 is being used to hide bad links
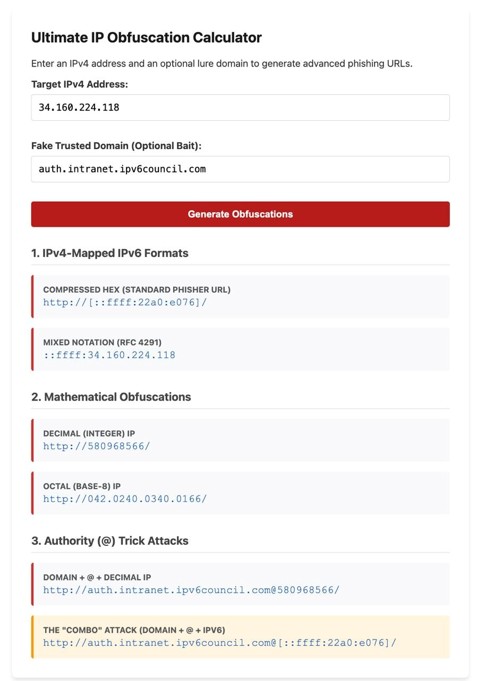
Attackers are using a standard IPv6 format to hide malicious links within phishing URLs. The trick is simple: they turn an IPv4 address into an IPv6-looking string, so the destination looks technical, unfamiliar, and easy to overlook. This is standard address syntax from RFC4291, while RFC5952 recommends a cleaner way to write IPv6 text.
The abuse is already happening in real-world situations. Malwarebytes recently discussed phishing emails that use IPv6-mapped IPv4 URLs to hide scam destinations, and SANS ISC also explained how these addresses work and why they are important. The key thing to remember is that even if the link looks unusual, it still points to a basic IPv4 host behind the scenes.
This isn’t about breaking IPv6; it’s about using proper syntax in a way that makes a malicious link less obvious to people and tools. When a filter only examines the raw string, or when someone quickly glances at the URL and sees brackets, colons, and hex digits, the attack gains an early edge.
We built a simple, standalone HTML/JS calculator to demonstrate how it works. What looks like an unusual IPv6 address can actually be a very normal IP address. That’s the main point: the misuse isn’t complicated; it’s just very effective.
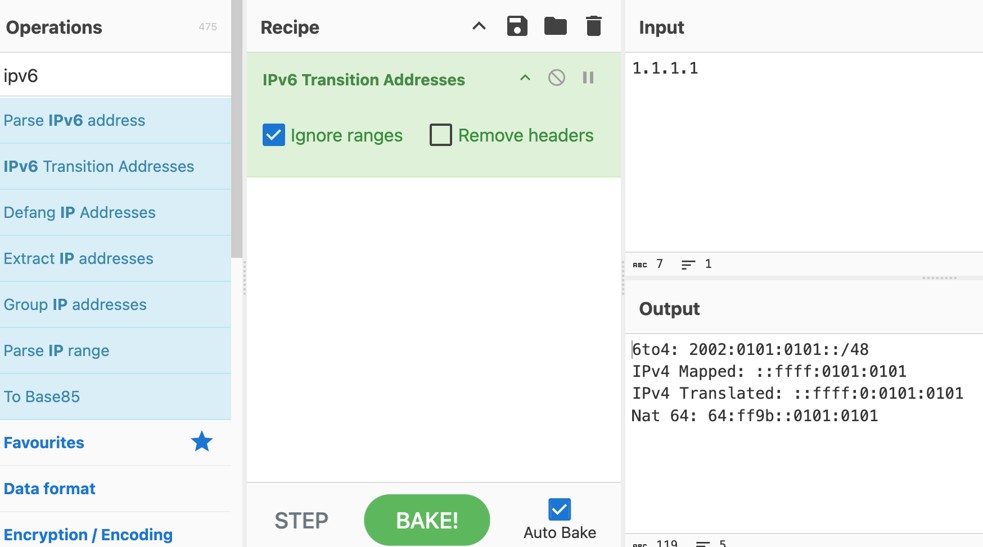
By the way, you probably know CyberChef, an open-source web-based tool for quick and easy data manipulation, encoding, encryption, and analysis. Fortunately, it’s included, so you can use it alongside all the other useful recipes in this versatile Swiss Army knife.
And that’s why phishing prevention, email security, and link inspection are so important. Security systems should start by normalizing the address and then verifying its real destination. Like humans, we shouldn’t trust a URL’s appearance until we’re sure of where it actually leads.